Trezor Login: Secure Access to Your Crypto Wallet
Everything you need to know about logging into your Trezor wallet safely and managing digital assets like a pro.
🔒 What Is Trezor Login?
Trezor Login is the process that connects your hardware wallet — the Trezor One or Trezor Model T — with your personal crypto dashboard. It provides an encrypted bridge between your device and the digital world, ensuring that your private keys never leave the hardware wallet.
Unlike online wallets or exchanges that store your data on cloud servers, Trezor Login gives you total ownership of your crypto. Your funds stay protected even if your computer or network is compromised.
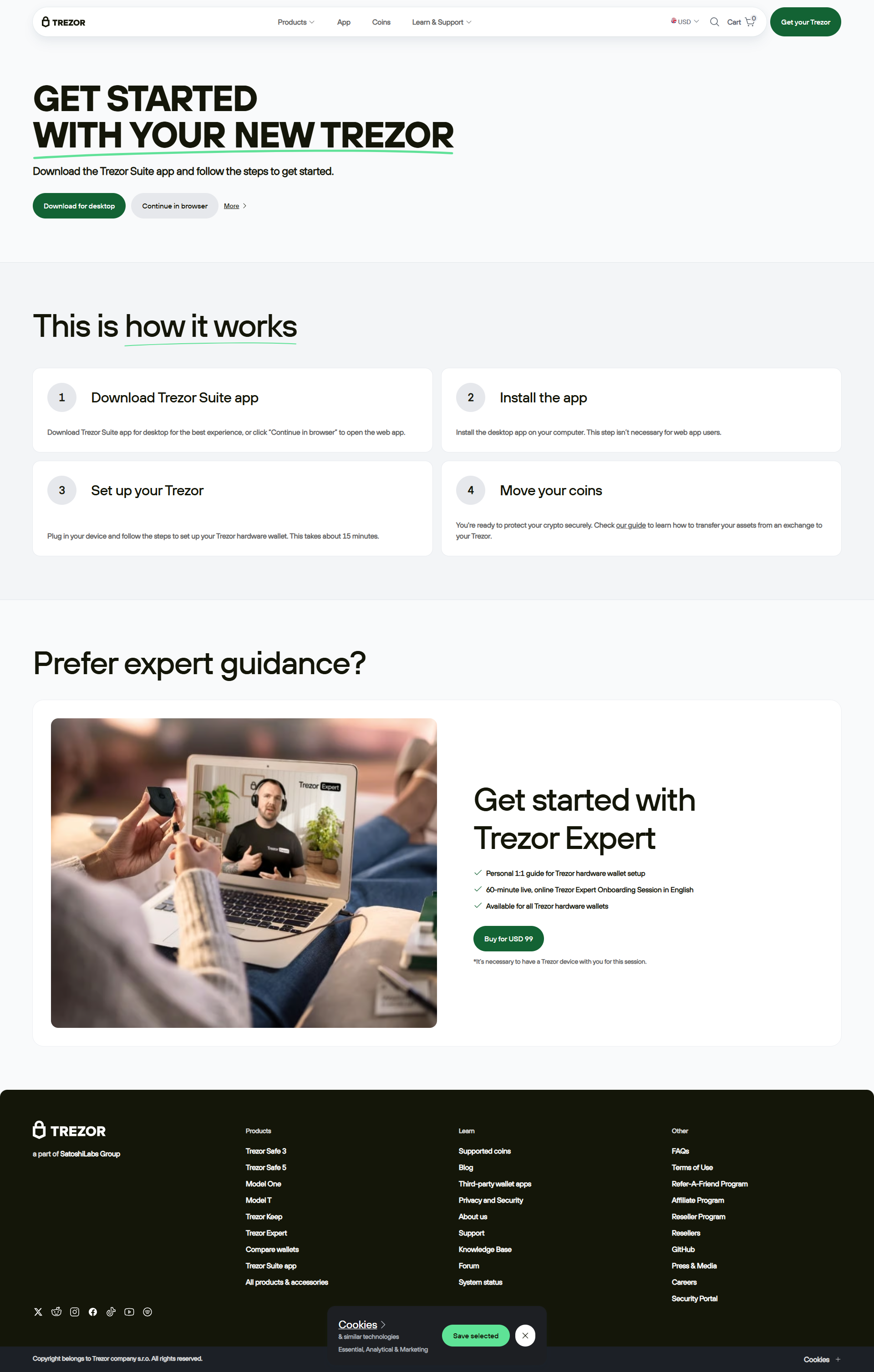
🧭 How to Access Your Wallet via Trezor Login
Follow these easy steps to access your Trezor wallet safely:
Step 1: Go to Trezor.io
Open your browser and visit the official Trezor.io website. Never click on ads or unofficial links.
Step 2: Access Trezor Suite
Click “Access Suite” to open the Trezor Suite app. It’s your main control center for portfolio tracking and transactions.
Step 3: Connect Your Device
Plug in your hardware wallet using a USB cable. The Suite automatically detects it and prompts for authentication.
Step 4: Enter Your PIN
Use your Trezor device screen to enter the PIN. This method prevents hackers from tracking your input.
Step 5: Access Your Crypto
Once verified, you can view balances, send tokens, and explore DeFi — all from your secure Trezor dashboard.
💡 Why Use Trezor Login?
Trezor Login doesn’t just make accessing your crypto convenient — it makes it bulletproof secure. Here’s why users trust it worldwide:
- 🧱 Hardware-level protection from online attacks.
- 🔐 Full control over your private keys — no third parties involved.
- ⚡ Intuitive design for beginners and pros alike.
- 🌐 Compatibility with Bitcoin, Ethereum, and 1000+ other coins.
- 🧩 Integrates easily with wallets like MetaMask for DeFi access.
📊 Comparison: Trezor Login vs Other Wallets
| Feature | Trezor Login | Exchange Wallet | Software Wallet |
|---|---|---|---|
| Security | Hardware Encryption | Custodial Risk | Medium |
| Key Ownership | User Controlled | Exchange Controlled | User Controlled |
| Offline Capability | Yes (Cold Wallet) | No | Limited |
| Supported Assets | 1000+ | Varies | Depends on App |
⚠️ Pro Tip: Avoid Phishing Traps
Always verify the URL before logging in. The legitimate Trezor website is https://trezor.io. Never share your recovery seed online or via email. Trezor staff will never ask for it.
❓ Trezor Login FAQ
1. Can I use Trezor Login on mobile?
Trezor Suite is designed for desktop, but you can access read-only balances on mobile browsers. Full mobile support is under development.
2. What happens if my Trezor device is lost?
Your recovery seed ensures you can restore your assets on a new device. Without it, no one — not even Trezor — can recover your crypto.
3. Is Trezor Login compatible with DeFi apps?
Yes. Through integrations with wallets like MetaMask and WalletConnect, you can interact securely with decentralized apps.
4. How often should I update my firmware?
Always install the latest firmware updates to ensure optimal performance and new coin support.
🔐 Final Thoughts: Take Control with Trezor Login
Trezor Login is more than just a way to access your wallet — it’s your foundation for crypto independence. With hardware protection, intuitive design, and cross-platform access, it empowers you to own your wealth securely and confidently.
Your keys. Your crypto. Your control — with Trezor Login.